Advanced Identity Manager based on Keycloak
In the new 3.0.0-jailbreak release, we have incorporated a new module with Identity Manager functionalities. This new module is built on the open source Keycloak solution.
In scenarios requiring a more complex and configurable identity management component, this module is intended to be a replacement for the current one (basic identity manager) which is based on Spring Security Oauth2.
Main advantages over the basic identity manager
- SSO: Single Sign On between multiple applications (including the Platform) through Oauth2/Open ID.
- Multiple user repositories: for the authentication process, it is possible to configure several types of user repositories simultaneously. By default, the Platform’s user repository is configured, but an LDAP, Kerberos, or even a customized one can be added by developing a small Java plugin.
- Identity brokering: in scenarios where you need to integrate the Platform with other client authentication servers, you can configure them through the identity brokering functionality, so that, using this module, you can authenticate yourself in other authentication servers in a centralized way and through a common interface (Oauth2/Open ID). An example would be a SAML 2 IdP, or a social IdP such as Google or LinkedIn.
- Advanced auditing: the auditing generated by this module is much more granular and is also integrated with the platform auditing, ready to be exploited.
- Advanced configuration of JWT claims: it is possible to configure extra claims in the JWT token generated for Oauth/Open ID authentication, where you can add extra attributes.
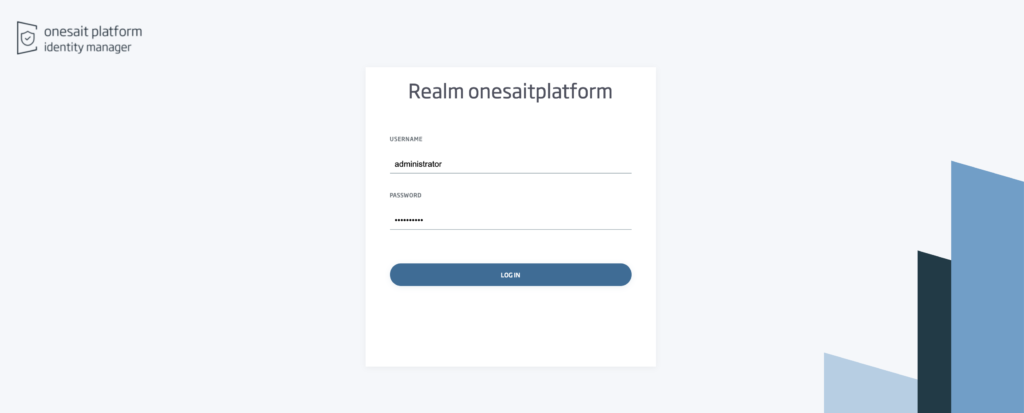
Transparent to the end user
For the end user, the existence of this module is transparent. When logging in, a log-in screen will appear with the same look-and-feel, indicating the Keycloak realm where the user is going to log in:
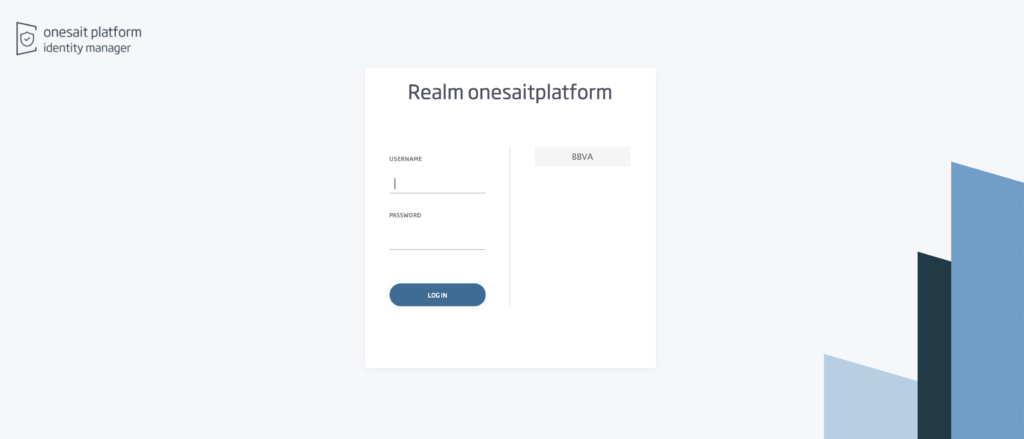
If there is Identity Brokering configured, then the user will see several methods for authentication:
Full integration with the Platform’s functionalities
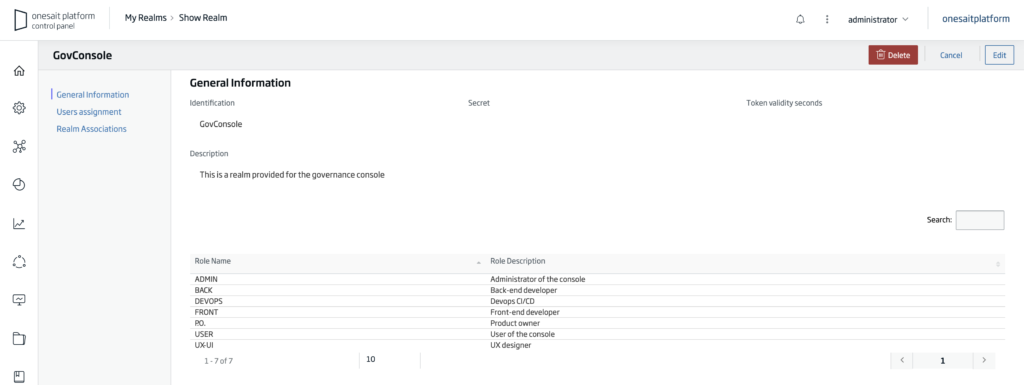
This module integrates with both the Multitenancy and Realm concepts of the Platform.
For each vertical of the existing Platform, there will be a Keycloak Realm, so that a specific and isolated configuration can be achieved for each vertical (different repositories, configurations, identity brokering, etc.).
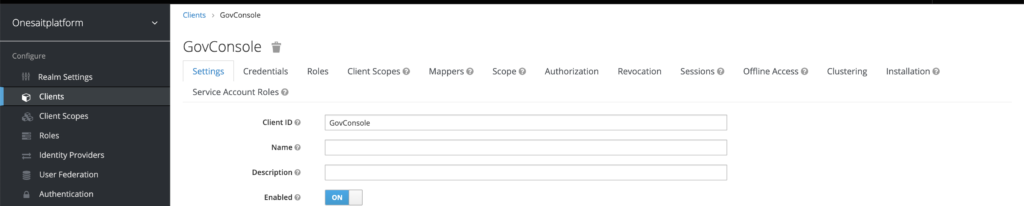
On the other hand, for each Platform Realm, a client is generated in the corresponding Keycloak realm, available to be used in the Oauth2/Open ID authentication process.
There is also IM-Platform synchronization so that, if there is any change in a Realm or Vertical, it is immediately reflected in the IM.
YouTube | Release 3.0.0 Feature – Advanced Identity Manager based on Keycloak