Analyzing Gartner’s Technology Trends for 2022
Every year, the Gartner Group publishes their list of main technological strategies, which you can download (after adding your email address) by filling this form.

In short, the tendencies that have been defined are the next:
- Tendency 1: Data Fabric
- Tendency 2: Cybersecurity Mesh
- Tendency 3: Privacy-Enhancing Computation
- Tendency 4: Cloud-Native Platforms
- Tendency 5: Composable Applications
- Tendency 6: Decision Intelligence
- Tendency 7: Hyperautomation
- Tendency 8: AI Engineering
- Tendency 9: Distributed Enterprises
- Tendency 10: Total Experience
- Tendency 11: Autonomic Systems
- Tendency 12: Generative AI
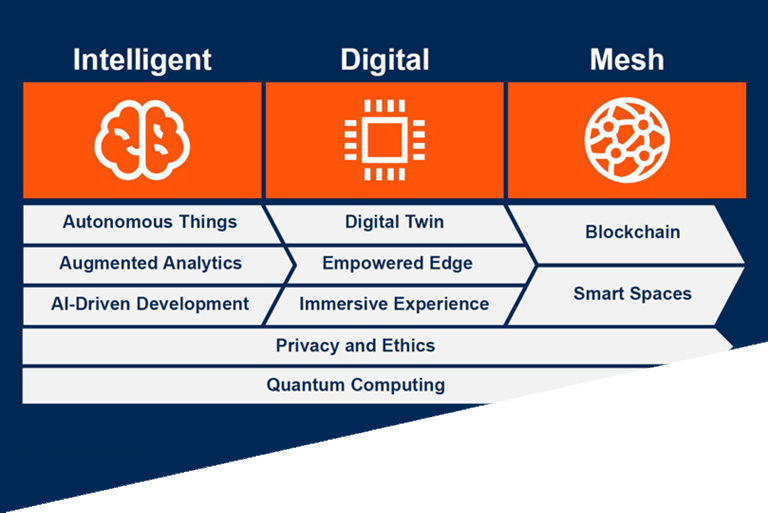
But, how were these categories defined? Well is based on three topics:
- Engineering Trust: considering that the technology needs a resiliant and efficient core, a well designed bases and that is trustworthy. In here they include:
- Tendency 1: Data Fabric.
- Tendency 2: Cybersecurity Mesh.
- Tendency 3: Privacy-Enhancing Computation.
- Tendency 4: Cloud-Native Platforms
- Sculpting Change: once a good bases has been stablished, the next goal are the technologies that allow the organization to extend their digitalization efforts. The job of IT is to provide the necessary tools so that the team can make changes. Here are included:
- Tendency 5: Composable Applications.
- Tendency 6: Decision Intelligence.
- Tendency 7: Hyperautomation.
- Tendency 8: AI Engineering.
- Accelerating Growth: once the foundations and building blocks of change are laid, is the moment to focus on technological tendencies that maximizes the value of what the organizations create to grow. Here we have this tendencies:
- Tendency 9: Distributed Enterprises.
- Tendency 10: Total Experience.
- Tendency 11: Autonomic Systems.
- Tendency 12: Generative AI.
How do we see it?
In a first look, we could be impressed by the way that Gartner categorizes these tendencies, but in reality, if we zoom-in over them, we can see that a lot of them are just different ways of naming tendencies that are already established, and that others are more of an aspiration than anything else.
Altho this opinion would apply to all these tendencies, where this zoom-in matters the most is the tendencies referring to «Engineering Trust» since these are the ones that compose the core of the technological strategy and somehow it seems like some of them were far away from that.
Let’s look at it in more detail.
Tendency 1: Data Fabric
The «Data Fabric» integrates the data between platforms and users, so the data has to be available when needed, with an approach that combines:
- Catalogue of expanded data.
- Graphic of knowledge enriched with semantics.
- Metadata activation.
- Recomendation Engine.
- Data Preparation and Delivery.
- Orchestration and DataOps.
According to Gartner, «a Data Fabric is capable of reducing the data management in a 70%», but on the other side, in their own reports, Data Fabric is more of a management and integration pattern for data than a product, and the implementation of a Data Fabric requires the combination of various data management technologies, both well-known and emergent.

On the other hand, the Hype Cycle for Data Management (2020), the Data Fabric has an estimated market penetration of 1% to 5% and is at the top of the Peak of Inflated Expectations. In addition, it has a horizon of five to ten years to reach full maturity, as some of the components are even less mature and therefore also have an even lower market penetration. For example, DataOps is still defined as an Innovation Trigger with a market penetration of less than 1%.
Tendency 2: Cybersecurity Mesh
Increasingly, digital business assets are distributed between the cloud and in data centers, leaving organizations at risk from traditional fragmented security approaches.

A cybersecurity mesh architecture provides a component approach to creating a scalable and interoperable service.
According to Gartner, organizations that adopt a Cybersecurity Mesh architecture to integrate security tools will reduce the financial impact of individual security incidents by an average of 90%.
Again we find normative statements rather than specific actions or products. Everyone knows that the number and nature of cyber threats are on the rise, and of course, we want «a composable architecture that integrates widely distributed and disparate security services».
Tendency 3: Privacy-Enhancing Computation (PEC)
PEC approaches allow data sharing between systems while preserving privacy. Approaches vary, but include encryption, splitting, or pre-processing of sensitive data to allow it to be handled without compromising confidentiality.
According to Gartner, we should expect that:
- By end of 2023, the 75 % of the global population will have their personal data covered by the modern privacy normatives.
- Until 2023, the organizations that can infuse digital confidence will be able to participate in more than 50% of ecosystems to amplify the oportunities of income increase.
- By 2025, 60% of large organizations will adopt privacy-enhancing computing (PEC) techniques for data processing in untrusted environments and multipart data analytics use cases.

And yet today in the PEC solutions arena we have a limited number of manufacturers with very specific and niche solutions, such as Concentric, Ketch or TripleBlind.
Tendency 4: Cloud-Native Platform
«Lift-and-shift» cloud migrations focus on taking legacy workloads and deploying them in the cloud. Typically, because these workloads were not designed for the cloud, they require a lot of maintenance and do not take advantage of any of the benefits.
Cloud-Native platforms offer elasticity and scalability in computing, reducing dependency on infrastructure to allow focus on application functionality.
According to Gartner, in 2025, Cloud-Native platforms will serve as the basis for more than 95% of new digital initiatives, compared to less than 40% in 2021.

Who could deny this trend? But it is not new either, perhaps the trend could be related to the strategies and platforms to make the lift-and-shift migration to the cloud.
And you? What do you think 2022 will bring us and how do you see it compared to Gartner’s opinion? We’ll be reading you in the comments.





Pingback: What can we expect from the IoT in 2022? – Onesait Platform Blog