Onesait Platform Information on vulnerability CVE-2021-44228
Regarding the CVE-2021-44228 vulnerability affecting the Apache Log4j library, the Onesait Platform team conducted an analysis on the 18th and 19th to see if Platform was affected, and the conclusions are as follows:
- Platform versions equal to or higher than 2.0.0-fireball (versions 2020 onwards) are not affected by this vulnerability (platform uses logback and there is no dependency with log4j2).
- In lower platform versions (versions prior to 2020) there is a dependency on log4j2, although the platform does not use the library and therefore the vulnerability is not exploitable.
Therefore, the platform is not affected by this vulnerability. By image we have considered removing the dependency on log4j2 in versions 1.3 to 1.6, and patches have been generated for these versions removing that dependency. Any project/product with an active subscription and one of these versions can request to update its version.
Additionally, as a contingency measure (not required), the JVM can be started with these 3 variables set to false:
-Dcom.sun.jndi.ldap.object.trustURLCodebase=false -Dcom.sun.jndi.rmi.object.trustURLCodebase=false -Dcom.sun.jndi.cosnaming.object.trustURLCodebase=false This can be done by adding the following environment variable in the CaaS:
JAVA_OPTS=-Dcom.sun.jndi.ldap.object.trustURLCodebase=false -Dcom.sun.jndi.rmi.object.trustURLCodebase=false -Dcom.sun.jndi.cosnaming.object.trustURLCodebase=false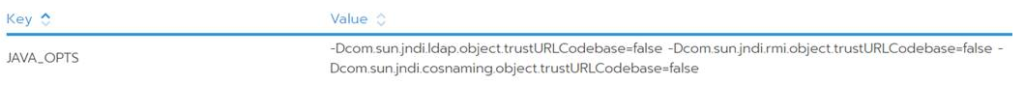
If you have any questions about it, please leave us a comment, or get in touch with us through the support channels.





Pingback: Vulnerability Management Pilot – Onesait Platform Community